ANALYSIS: Making sense of the WikiLeaks CIA hacking exposé
Key take-aways from the latest WikiLeaks document dump.
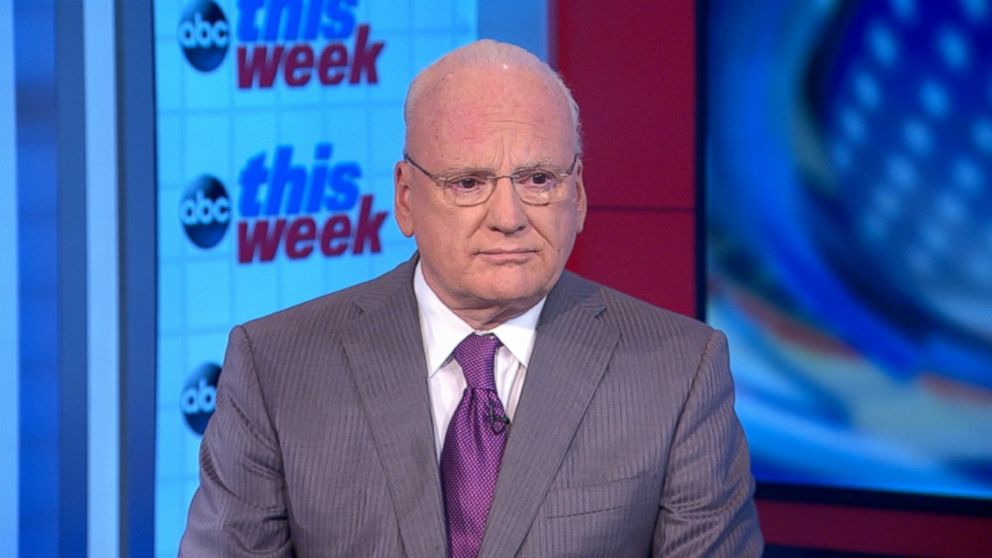
ABC NEWS CONTRIBUTOR – WASHINGTON — -- Richard Clarke was the Special Advisor to the President for Cyberspace in the George W. Bush administration and is the author of the book Cyber War. Today he is an ABC News contributor on national security issues.
Coming in the flood of news stories that have bombarded us for the last month, the revelation of CIA hacking activities and tools on WikiLeaks may seem like just another chapter in a fast-paced spy novel that is unfolding all around us. For Americans trying to make sense of it all, however, here are a few take-aways.
Inadequate internal security
First, the fact that Top Secret CIA documents are available for all the world to see proves yet again that the intelligence agencies have not yet implemented adequate internal security.
After NSA documents were leaked by Edward Snowden, President Obama empaneled a group of outsiders (including me) to advise him on, among other things, how to stop such leaks in the future.
The recommendations of that group on how to plug the leaks have not been fully implemented at all US intelligence agencies. Too many people, including contractors, have access to information that they do not need to know. Too few controls on documents have been utilized. Existing technology would have allowed CIA to track and control every copy of sensitive documents, but such security measures were not used.
No domestic spying
Second, nothing in the documents posted on line indicates that CIA was spying on Americans or doing anything beyond what it is legally chartered by Congress and the President to do.
The WikiLeaks release proves only that CIA spies, including electronically, which is what it was established to do. In the past spying meant physically stealing papers and photographing them.
Today, spying means getting on to electronic devices like iPhones and, yes, televisions used by terrorists, drug cartels, sellers of weapons, and hostile government officials.
It is done to keep us safe and we should only have a complaint if it were not being done against such targets.
Vulnerability in your pocket
Third, almost any electronic device can be penetrated and any cyber defense subverted by a determined hacker, especially one with a budget in the billions of dollars.
It is much harder and more expensive to defend than to attack in cyberspace.
New defenses, such as encrypted messaging apps, only protect for a short time before hackers find a way to defeat them.
Hoarding flaws
Fourth, under presidential policy approved by Barack Obama, government agencies that find flaws in generally available commercial software are supposed to inform the White House.
Then an interagency group is supposed to recommend whether to tell the software manufacturer, or, if there is an over-riding intelligence need to exploit the flaw, to collect information using the flaw for a short period of time.
The WikiLeaks documents would suggest that CIA was hoarding knowledge of flaws in software on things like Android phones for its own use, rather than sharing that knowledge with the White House and the software manufacturer.
The Obama policy stemmed from a realization that if we know about software vulnerabilities, so will Russia, China and others who will exploit the holes in the code to steal from US corporations and agencies.
Obama reasoned correctly that we were better off defending ourselves than in attacking others.
Assange and Russia
Fifth, Julian Assange, the man behind WikiLeaks, appears to have a strong relationship with Russia.
I would not automatically believe his claims about where he gets his information, or indeed about anything.
He claimed that the files of the Democratic National Committee he posted to WikiLeaks last summer were not originally hacked by Russian intelligence, when actually there is very good reason to believe Russian agencies stole those files.
When he tells us now that the CIA files in this release were obtained from a government contractor, he may be right. It is equally plausible that Russian intelligence hacked into a CIA laptop somewhere and passed them to their "friend," Assange.
The release of the CIA materials greatly strengthens the hand of the Russian propaganda machine by seeming to prove correct many of the claims it has been making around the world about the “nefarious” CIA.
Exposing an alleged CIA hacking base in Germany fits right in to the Russian campaign to weaken support for NATO and the U.S. in Germany.
All in the timing
Sixth, the timing of the WikiLeaks postings is of note.
They come after the alt-right “news media” have been suggesting that perhaps “deep state” agencies like FBI and CIA are in league to destroy President Trump by – among other things – saying that Russia hacked the US election.
The new WikiLeaks documents claim that CIA sometimes hacks and makes it look like the attack was Russian. The alt-right immediately leaped on that claim to cast doubt on the conclusion by 17 U.S. intelligence agencies that Russia tried to help Trump get elected.
Even some people in U.S. intelligence not usually given to conspiracy theories are thinking that – like the Wikileaks exposure of the DNC files – this new expose seems to be timed by Russian intelligence for political effect in the U.S.
Cyber war takes many forms, not just the damage and destruction of physical objects connected to the internet.
When the Russians play cyber war, it can be the damage and destruction of trust and truth.



