What we know about the kill switch in Petya ransomware attack
U.S. researcher has found a temporary "vaccine" against the attack.
MOSCOW— -- Cybersecurity researchers have been racing to analyze the new ransomware that struck Tuesday, first hitting Ukraine in an avalanche of attacks before spreading to other countries around the world.
The malicious software has been identified as a modified version of a previously known ransomware, called Petya or Petrwrap, that has been substantially altered, prompting a debate among researchers over whether it is new malware.
Here’s what we know:
How the malware works
The malware works by encrypting a computer’s hard disk, locking out users and then posting a ransom demand telling them to pay $300 to a bitcoin account to unlock it.
At first glance, it resembles WannaCry, ransomware that locked users out of hundreds of thousands of computers in May, but researchers have already noted some crucial differences.
Petya is a so-called worm, meaning it has the ability to self-propagate. It does so by building a list of target computers and using two methods to spread to those computers, according to U.S. software company Symantec.
"A worm knows no geographic borders," Jeff Greene, senior director, global government affairs and policy at Symantec, said.
A key difference is that, unlike with WannaCry, researchers have not been able to find a so-called kill switch that would shut down the malicious code globally. But researchers believe they have found a temporary means of disabling the malware on individual computers.
One U.S. cybersecurity researcher, Amit Serper of Boston-based Cybereason, identified a fix on Tuesday night, and other researchers have termed it a potential “vaccine,” or localized kill switch for the malware. By changing a single file name, Serper found, users can trick the malware into shutting down on their computers.
His method has been confirmed by several other firms, but he warned that it is only a temporary fix because large-scale attacks normally occur in several waves and hackers may easily change the file names, making the “vaccine” ineffective against the malware.
Understanding the nature of the malware
Analysts are still debating the nature of the malware. Petya has been known to cyberresearchers since 2016. But some believe the malware that struck Tuesday has been significantly modified, to the extent that it is new malware, prompting some to nickname it NotPetya.
In light of the debate, cybersecurity news portal BleepingComputers termed it SortaPetya.
What most researchers agree on is that the malware uses a tool developed by the U.S. National Security Agency and stolen by hackers.
Symantec and other firms said the ransomware infects computers through an exploit termed EternalBlue, which takes advantage of a vulnerability in Windows operating systems. That same tool was used by WannaCry and was among a vast trove of cyberweapons stolen from the NSA last year by a group of hackers called the Shadow Brokers, which published the weapon online in April.
The use of the tool in a second major cyberattack in two months has prompted criticism of the NSA for losing control of the weapon.

After WannaCry, Microsoft issued patches for its Windows versions back to Windows XP that blocked the vulnerability; computers updated with that patch are protected from the new attack.
WannaCry was stopped after a young cybersecurity researcher in Britain stumbled across a kill switch embedded in the malware. It was considered at the time an unlikely stroke of luck, abruptly curtailing the malware as it was racing into new networks.
Petya/NotPetya’s ransom message lists a Posteo email address where a message confirming the ransom payment is meant to be sent. But the email provider, a German company, quickly closed the account, in theory making the payments impossible. So far, the hackers have received only a few thousand dollars in ransom, according to Wired.
Debating the hackers’ intentions
Ukraine’s cyberpolice agreed that an update to ME-Doc software played a key role in unleashing the attack, noting in a statement that the update, far larger than those usually sent, went out around 10:30 a.m. local time to companies, with the malware multiplying from there.
Police officials said they believe the hackers unwittingly used ME-Doc.
Some people have described the attack as targeting Ukraine, with computers in other countries affected only as collateral damage, while some researchers have suggested that the attack was intended to cause damage rather than collect ransoms.
Nicholas Weaver, a senior researcher at the International Computer Science Institute, told the cybersecurity blog Krebs on Security that he believes it was possibly an attack “disguised as ransomware.”
“I’m willing to say with at least moderate confidence that this was a deliberate, malicious, destructive attack or perhaps a test disguised as ransomware,” he added.
Analysts were split on that theory, however.
How to fight the malware
Meanwhile, no kill switch has been found for Petya/NotPetya. Serper’s fix can rescue some individual machines.
To implement the fix, users should create a file called Perfc in the C:\Windows directory but without the file extension DLL that the malware contains. When the malware encounters the file, it’s tricked into quitting, stopping the encryption.
Serper was surprised that the fix worked. He was on vacation in Israel when the attack began, he told ABC News by phone Tuesday.
“I had, like, three hours earlier where I had nothing to do, and I started reverse-engineering that malware,” he said.
He modified the malware in his parents’ living room as they sat and watched TV, he added, and he later talked another researcher through the process while at a bar with friends.
A hero among cybersecurity workers
Seper has become a minor hero among cybersecurity workers after posting his method on Twitter. “I even got 35 job offers,” he said.
But he warned that the fix is only partial and could quickly be circumvented. “This only stops this current outbreak,” he said. “If there will be another outbreak like WannaCry, where they had several waves of these attacks, they will probably change the name of the DLL, or they might as well change how the function works.”
Who’s been affected
The attack spread rapidly Tuesday, hitting some of the world’s largest companies, including Danish shipping giant Maersk, the French multinational construction materials firm Saint-Gobain and U.S. pharmaceutical firm Merck & Co.
The top five countries affected by the ramsomware are Ukraine, the United States, Russia, France and the U.K., according to Symantec.
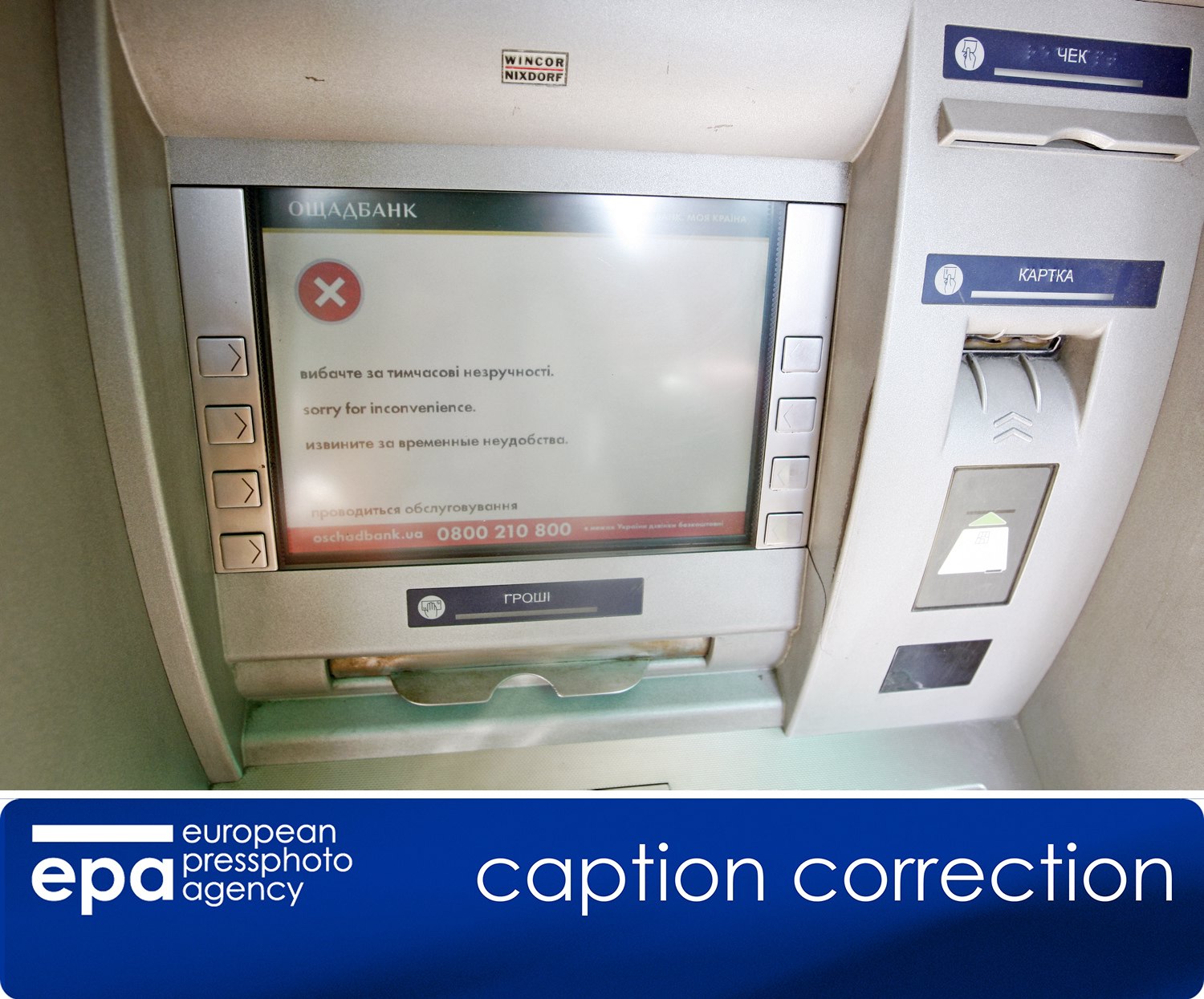
There are questions about why the attack disproportionately hit Ukraine and Russia. Russian cybersecurity firm Kaspersky Lab, which congressional sources told ABC News is itself under FBI scrutiny, found that about 60 percent of infections occurred in Ukraine. There, ATMs were frozen, people found cash desks at some supermarkets, and post offices were blocked.
Ukraine’s administrative Cabinet of Ministers said its office computers were hit, and a number of large banks, the state railway system, Kiev’s chief airport, an energy company and several telecom providers were reportedly struck.
Even radiation monitoring at the destroyed Chernobyl nuclear power station was affected, with technicians forced to carry it out manually after their Windows computers were locked, Ukraine’s government said.
Russian companies were also hit by the malware. The state-owned giant Rosneft tweeted that it suffered a major cyberattack around the time the ransomware outbreak was reported. The Russian business newspaper Vedomosti posted photographs of ransom screens sent by workers at another oil company, Bashneft, which Rosneft owns.
Group-IB, a Moscow-based cybersecurity firm, reported that at least 80 companies were hit in Russia and Ukraine. Russian steelmaker Evraz said its systems were affected, according to the state news agency RIA Novosti. The Russian branch of a pet food producer owned by the U.S.-based Mars candymaker also reported an attack.
Ukrainian officials were quick to blame the attack on Russia, whose hackers have been linked to serious cyberassaults on critical infrastructure in the country. Those did not involve ransomware, however, and it is unclear who was behind Tuesday’s attack.




