British Intelligence Gives 'Anonymous' a Taste of Its Own Hacking Medicine
Edward Snowden leaks another document showing agents also posed as hackers.
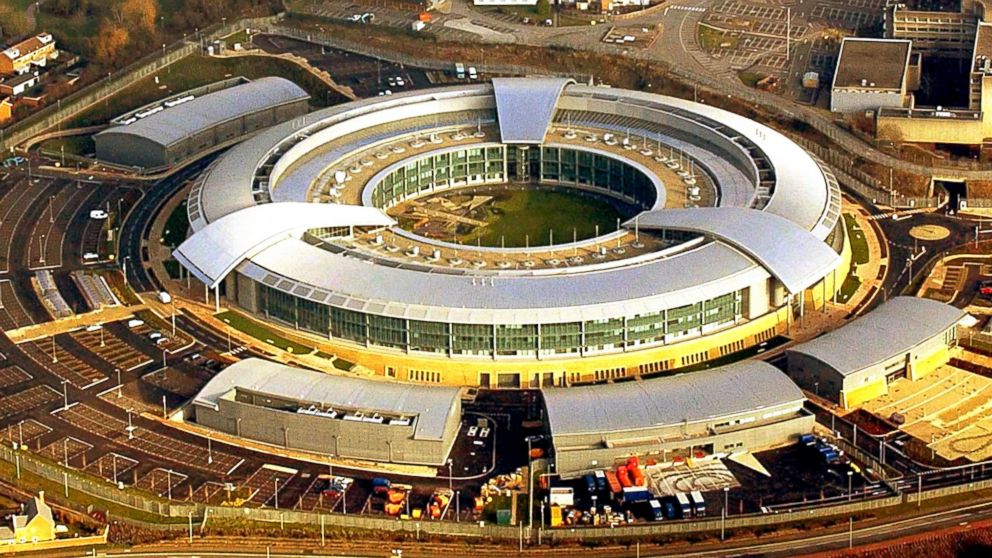
Feb. 6, 2014— -- Both the NSA and its British counterpart, the GCHQ, were revealed to have been capable of figuring people's identities by tapping into your smartphone app activity.
Now, a classified presentation prepared by GCHQ and leaked by Edward Snowden show that the GCHQ and its partners are up to more than just surveillance. The documents were first published by NBC News.
The Joint Threat Research Intelligence Group (JTRIG) specifically had its sights set on Anonymous, the infamous activist hacker group. Anonymous has a record of temporarily disabling several organization's websites, such as the CIA and the Church of Scientology. One of the ways it does so is through using a Distributed Denial of Service attack, or DDoS.
The leaked documents show that the JTRIG was ready to fight fire with fire, launching the operation "Rolling Thunder." JTRIG agents issued their own DDoS on Anonymous chat rooms, preventing its users from communicating with one another.
JTRIG reached out to Anonymous members through email, Facebook and other means to warn them that "DDoS and hacking is illegal, please cease and desist," according to NBC News. JTRIG reports that one month after the attack and the warning, 80 percent of those users were no longer in the Anonymous chat room.
The leaked presentation also highlights interactions with specific members of Anonymous. JTRIG credits one conversation to the arrest and conviction of Edward Pearson, who went by the username Gzero, for stealing over 8 million identities and information from 200,000 PayPal accounts.
Hackers and activists have criticized the GCHQ's usage of a DDoS as a double standard. Jake Davis, a former hacker affiliated with Anonymous, was recently released from prison after pleading guilty to two counts of DDoS.
"All of GCHQ's work is carried out in accordance with a strict legal and policy framework," GCHQ said in a statement. "All of our operational processes rigorously support this position."




