Why ransomware cyberattacks are on the rise
A recent spate of ransomware attacks has left the nation reeling.
What often begins as an employee clicking a seemingly innocuous link in their email can result in a crisis that brings multibillion dollar businesses to their knees, stokes geopolitical tensions and has ripple effects throughout the global economy.
A recent spate of ransomware attacks has crippled critical American infrastructure, disrupted major food supply chains and revealed that no firm -- big or small -- is safe from these insidious cyberattacks.
Ransomware strikes have surged over the past year due to a confluence of factors, experts say, including the rise of hard-to-trace cryptocurrency, a work-from-home boom that has resulted in new IT vulnerabilities and a political climate marked by ongoing tensions between the U.S. and Russia -- the nation from which many of these attacks are believed to emanate.
The recent attack on Colonial Pipeline, operators of one of the United States' largest fuel conduits, also showed that victims are forced to decide between paying criminals their ransom demands or being unable to operate their businesses. The cyberattack led to a multiday shutdown for the pipeline that provides nearly half of all fuel consumed on the East Coast. As a result, panic-buying pushed gas prices to their highest levels in seven years just ahead of Memorial Day weekend travel.
Ultimately, Colonial Pipeline made the decision to pay a ransom of $4.4 million in cryptocurrency to DarkSide, the Eastern European criminal organization the FBI said is behind the attack.
"This decision was not made lightly," the company told ABC News in a statement, but said it was "one that had to be made."
"Tens of millions of Americans rely on Colonial -- hospitals, emergency medical services, law enforcement agencies, fire departments, airports, truck drivers and the traveling public," the Georgia-headquartered firm added. "Our focus remains on continued operations to safely deliver refined products to communities we serve."
Just a few weeks later, as some analysts still mulled over whether the payout set a bad precedent, the world's largest meat processor, JBS, was hit by a cyber assault involving ransomware.
JBS revealed that it had been the target of an "organized cybersecurity attack" that a White House spokesperson confirmed involved a ransom demand from a "criminal organization likely based in Russia."

Who is behind these attacks and why?
Several of the recent ransomware attacks are suspected to come from Russia and Eastern Europe, authorities have said. The FBI -- the agency leading the investigations -- has attributed the JBS attack to Russia-based hacking groups REvil and Sokinokibi, and the Colonial Pipeline breach to the Eastern Europe-based criminal organization DarkSide.
The U.S. cybersecurity community and government officials have not ruled out Russia as a major player behind the recent large-scale cyberattacks. Russian intelligence has also been known to cooperate with Eastern European cybercriminals in the past, U.S. cybersecurity authorities say.
"I don't think we've seen a period of this kind of high-intensity cyber operations from Russian soil directed against a variety of different U.S. targets arguably ever," Javed Ali, a former National Security Council director of counterterrorism, told ABC News.
"The fact that this kind of activity is happening with a relatively high frequency and also all signs sort of leading back to Russia, that is very disturbing," Ali added.
Experts say there are two primary motivations behind ransomware attacks: political and financial.
"I think the motivation of the individuals is financial; the motivation of Russia for allowing these groups to exist is partially political," said Alex Stamos, former chief security officer of Facebook and current adjunct professor at Stanford University's Center for International Security and Cooperation, as well as a partner at Krebs Stamos Group.
"There is a nonzero economic impact here of having billions of dollars stolen from companies around the world then flow into the Russian economy," Stamos added.
Cryptocurrency's role in ransomware
Helping to drive the financial motivation for ransomware attacks is cryptocurrency.
"The thing that really kept people from making tens of millions of dollars doing hacking 10, 15 years ago, is it's very hard to get money out of the international banking system," Stamos said.

Cryptocurrency, Stamos said, is easy for companies to purchase. Hackers know this and leverage that when holding data for ransom.
The rise and mainstream push of cryptocurrency is also tied to "the capability of these guys to get paid off," according to Stamos.
Sergey Pavlovich is a former cybercriminal who was indicted by the U.S. Department of Justice in 2008 as part of hacker ring that stole 40 million payment card numbers. He spent 10 years in jail in his native Belarus. Now, he hosts a popular YouTube show in Russia, where he talks about the cyber underworld and gives tips on how to avoid being hacked.
Pavlovich said it is hard for U.S. authorities to prosecute Russian hackers.
"We have a good saying here -- if you don't steal in Russia, you have no problems, and this is true," he told ABC News. "Because all attempts by the American government, for example, to extradite some person from Russia are not successful."
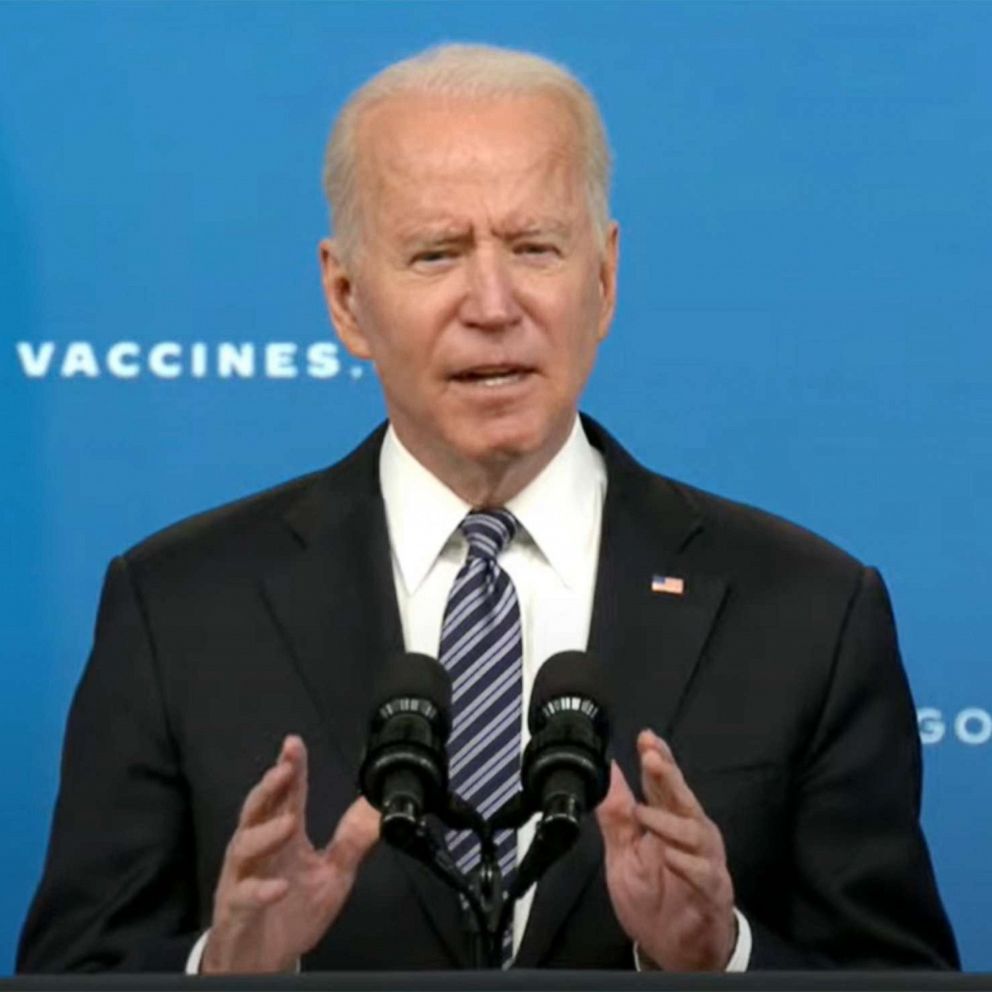
White House press secretary Jen Psaki said the recent attacks will likely be discussed when President Joe Biden and Russian President Vladimir Putin meet face-to-face later this month.
Stamos added that ransomware hackers are "effectively conglomerate platforms, of which they provide a bunch of different tools, and then they allow affiliates to do the work on top of them."
He added that they have increasingly seen "the creation of this hub-and-spoke model, where a number of different groups are effectively ransomware-as-a-service providers."
Ready-made ransomware
Ransomware-as-a-service refers to a business model where ransomware variants are leased to cyber criminals.
"And then that means the number of people who can do it effectively has grown significantly," Stamos said.
Ready-made software and utilities exist on the so-called "dark web" that a tech-savvy user could access to bring a company's productivity to a standstill, according to Dr. Vikram Sethi, a professor, cybersecurity researcher and the former director of the Institute of Defense Studies and Education at Wright State University.
"This phenomena of working from home has created a new generation of hackers and miscreants who are using their time to do this," Sethi said. "The time is there, the opportunity is there."
"The number of software and tools that are being readily made available on open sites that people can download and use has risen dramatically," he added.
How do ransomware attacks happen?
Ransomware attacks are made possible the same way as other cybersecurity breaches, experts say. Businesses with internet-connected devices not updated with the latest software updates (often referred to as "patches") and users who wantonly click on any link that comes through their emails contributes to malware taking root into a company's networks.
That malware is the entry point for ransomware attacks, according to Stamos.
"That person clicks on a link, or they open up a document, and then the malware starts on their computer and spreads," he said.
In other cases, hackers are "breaking in through interfaces that are still exposed publicly."
"It has come out that there are a number of services that were exposed publicly in the Colonial Pipeline [hack]," he added. "It looks like they might have had [Microsoft] Exchange servers that have not been patched."
How can firms respond and how can attacks be prevented?
Some recent high-profile ransomware attacks have been resolved by capitulation and big payouts. The University of California, San Francisco said last summer that it paid $1.14 million in ransom to hackers behind a malware attack.
Also last year, Travelex reportedly paid its hackers a ransom of $2.3 million, The Wall Street Journal reported. And most recently, Colonial Pipeline admitted to paying out some $4.4 million.
Despite these incidents, authorities still urge against paying ransom to hackers.
"Paying a ransom doesn't guarantee you or your organization will get any data back," the FBI states on its website. "It also encourages perpetrators to target more victims and offers an incentive for others to get involved in this type of illegal activity."
But for businesses, especially those like Colonial Pipeline that provide crucial services, time spent trying to negotiate or outwit hackers can mean huge financial losses and other detrimental business consequences.
"The FBI will generally ask you not to pay, but they don't have any legal authority to stop you from doing so," Stamos said.
Stamos, in his work with his partner Chris Krebs, the former director of the Department of Homeland Security's Cybersecurity and Infrastructure Security Agency, is exploring a number of proposals for dealing with ransomware in business. One, he said, is requiring businesses to report ransomware attacks.
"There's a number of companies that this happens to, they never report [to] law enforcement, they just pay the ransom, and everybody goes along their merry way," Stamos said. "We need to make it a legal requirement that you have to disclose when you get the threat."
Biden signed an executive order in the wake of the Colonial Pipeline saga that aims to improve communication between the private sector and law enforcement regarding cyberattacks, but stops short of mandating firms share information if they don't do business with the federal government.
"And then people go as far as saying we should outlaw any kind of ransomware payments," Stamos added. This could be enforced by adding ransomware crews to the list of terrorists or other groups that the Treasury Departments's Office of Foreign Assets Control bars Americans from doing business with.
As for preventing these types of attacks, Sethi said there are things businesses and their employees can do.
"First we've got to increase our own awareness," he said. "Sometimes we just pretend that because we are small, people will bypass us, and that's not true."
"If you haven't been attacked, consider yourself lucky," Sethi added.
Basic cyber education for employees is crucial, Sethi said, such as teaching people not to click on links from unknown senders.
Companies' IT departments also need to make sure that software updates and patches are regularly installed, he added.
"Most of those small-midsize companies can't afford to have an IT security person on staff," Sethi said. "But there are ways around it by using the services of a group of individuals."
Just by having someone check to make sure everything is updated once a week or so "will reduce the incidence of such things within your organizations dramatically."
"It's small, but ongoing, relentless steps that can keep us safe more than just one big thing," Sethi added.